Search Button browser hijacker is endorsed as a useful tool that offers a customized search engine which can be used professionally. However, in reality, it is a piece of rogue software which belongs to the family of browser hijackers. After silently infiltrating the targeted Windows computers, it makes modifications to the default web browser settings to promote a fake search engine (keysearchs.com).
The main purpose of developers behind Search Button browser hijacker is to redirect user search queries to various dubious/ malicious websites so that they can earn advertising revenue.
So, if your search queries are also keep getting redirected to questionable sites through keysearchs.com, then you are advised to get rid of the Search Button browser hijacker as quickly as possible. This guide is aimed to help you remove this annoying browser hijacker from your computer and reset your internet browser to its original settings.
What is Search Button?
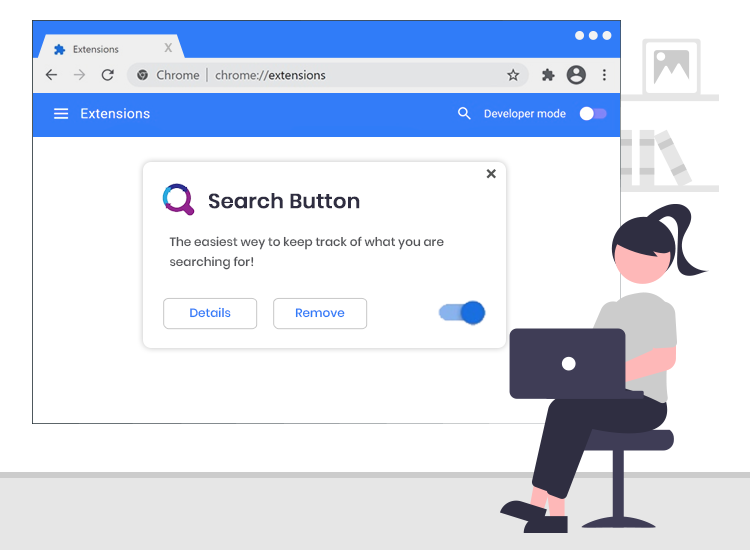
As said earlier, this is a piece of rogue software classified as a browser hijacker. Since most users install Search Button and other software of this type inadvertently, they are also categorized as potentially unwanted applications (PUAs).
Following successful installation, Search Button replaces the default homepage and search engine of your web browsers (e.g., Chrome, Firefox, and Edge) with its own customized search engine (keysearchs.com). Additionally, this rogue app is capable of collecting the following personal and browsing-related details.
- Entered search queries
- Geolocations
- IP address
- Usernames
- Passwords
- Credit card information, etc.
Common Symptoms of Search Button Browser Hijacker
You may notice the following symptoms if you have this browser hijacker installed on your laptop or desktop computer.
- Your preferred search engine and the home page are replaced by keysearchs.com.
- Browser is showing misleading search results.
- Searches getting redirected to unfamiliar websites.
- Websites are taking more time to load.
- A barrage of pop-up advertisements alerts.
How to Remove Search Button Browser Hijacker?
To completely remove this browser hijacker and other rogue applications without performing several tedious steps, we recommend running an automatic scan with a reputable antivirus/ anti-malware software on the infected computer.
Furthermore, we urge you to implement the below-mentioned cybersecurity practices to protect your computer against a range of cybercrimes.
- Carefully read the license agreement before downloading/ installing software.
- Avoid opening email attachments from unknown sources.
- Always keep your operating system and software applications up-to-date.
- Create strong and impossible-to-guess passwords.

