OS command injection is one of the most commonly found internet threats. The internet spectrum is filled with a lot of vulnerabilities and loose ends which gives easy entry to these malicious programs.
What is OS Command Injection?
Also known as shell injection, an OS command injection aims at exploiting web security vulnerabilities. It is used by hackers to conduct arbitrary OS commands on the applications server and infect the data and applications attached to it. In addition to this, cyber criminals also use it to compromise the other participants on the main hosting infrastructure.
How Does An OS Command Injection Work?
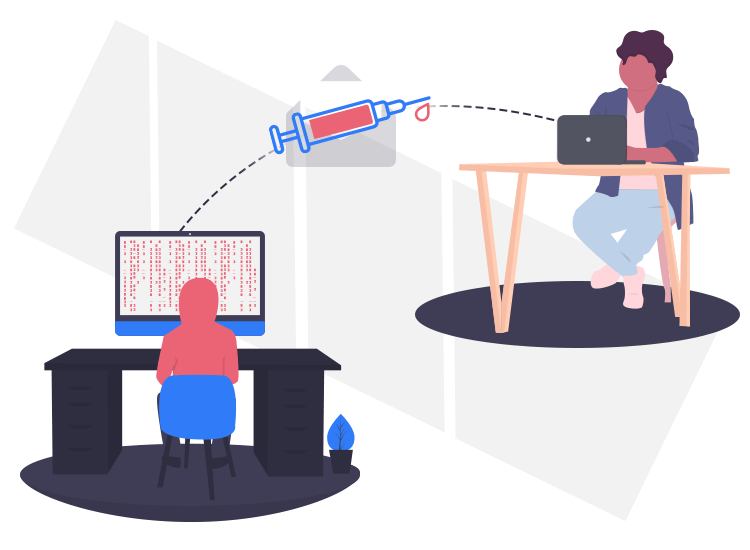
The first steps involve identifying the vulnerabilities in the network of the application. The attackers insert a malicious code to gain access to the functionality that the application offers.
Secondly, the hackers use an HTML code to alter the content on the web page with the help of cookies or form fields. Once the code is successfully injected into the compromised web page, the related web-browser interprets the code.
This entire process will help the hackers to execute an infected command on the user’s device, users network along with the network of the infected device.
The Consequences of an OS Command Injection Attack
- It can break the application’s website.
- It allows attackers to execute arbitrary commands to gain elevated privileges.
- I can also give unauthorized data access to hackers.
- It may fully infect the hosting infrastructure.
- In addition to this, it also allows hackers to gain full access to other systems within the organization that is attached to the same network.
Preventing Damage
- The first and foremost step that one should take to mitigate the damages, is to completely cut-off the connection of the compromised application. This will prevent the hacker from accessing the other vulnerable scripts.
- Applications that are accessible through a web browser should avoid using user-controllable data.
- Rejecting unacceptable codes can also be used as a preventive measure. It means that the development teams should create a whitelist of all the acceptable values. If during the validation process the user’s data falls outside the defined acceptable values it should be automatically rejected.
- In addition to this, a powerful input validation process should be followed that includes validation of all Alphanumeric characters and number validation.

