Nowadays cybercriminals create new computer viruses and other types of malware nearly every day and one of them is Con30 ransomware. This ransomware-type infection belongs to the well-known Dharma ransomware family. It is one of the most devastating malware threats to home and business users alike. That’s why we’ve prepared this step-by-step article to guide you through the process of what to do in case the system is infected by this nasty Con30 ransomware infection.
What is Con30 Ransomware?
Con30 ransomware is a type of data-encrypting malware. Like all ransomware-type infections, this one penetrates the security vulnerable system, encrypts all types of (images, videos, work documents, etc.) files using cryptographic algorithms, and demands a ransom payment for the decryption.
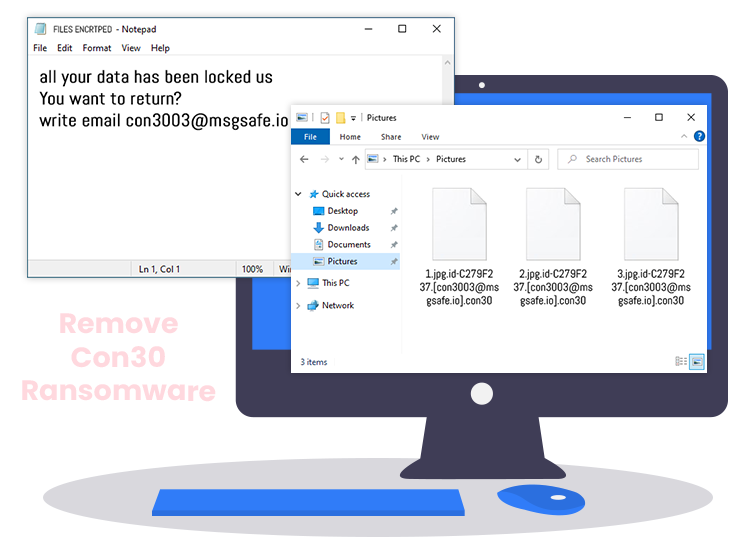
During the encryption process, Con30 renames the affected files with the following pattern: original filename, unique ID assigned to the victims, con3003@msgsafe.io email address, and the “.con30” extension. For example, a file originally named “1.mp3” would appear as something similar to “1.mp3.[9B83AE23].[con3003@msgsafe.io].con30” after the encryption is completed.
To alert victims about the encryption, it creates a ransom note named “FILES ENCRYPTED.txt” and drops it into every compromised folder. The ransom-demanding message contains detailed instructions on how to contact the attackers and pay a ransom fee in order to get decryption keys/software.
Con30 Ransomware: Distribution Techniques
Cyber crooks use various techniques to inject malicious programs like Con30 ransomware into the targeted systems. Below are some of the most common ones:
- Malicious links or infected email attachments
- Intrusive online advertisements or illegitimate software updaters
- Exploit Kits
- Unofficial and dubious download sources
- Adult content and pornographic websites
- Peer-to-Peer sharing networks (e.g., BitTorrent)
- Flaws of outdated software
How to Remove Con30 Ransomware from PC?
The manual threat removal process is quite time-consuming and also requires a certain level of computer skills. Therefore, it is suggested to use a trusted and powerful antivirus/ anti-malware program to automatically detect and remove Con30 ransomware and other types of malicious programs from your computer.
Along with this, you are advised to follow the below-mentioned security tips to protect yourself online and prevent data thieves and hackers from getting inside your system.
- Don’t open, download, or execute any files or email attachments from someone you don’t know.
- Keep your computer’s operating system and other installed software up-to-date.
- Avoid using free public Wi-Fi networks or hotspots.
- Make sure your passwords are strong and harder for data thieves to crack.
- Backup your precious data to external storage devices (e.g., USB thumb drive).

