An IRC worm (Internet Relay Chat Worm) is a malicious program designed to exploit IRC channels to infect chat rooms and message forums by sending infected messages.
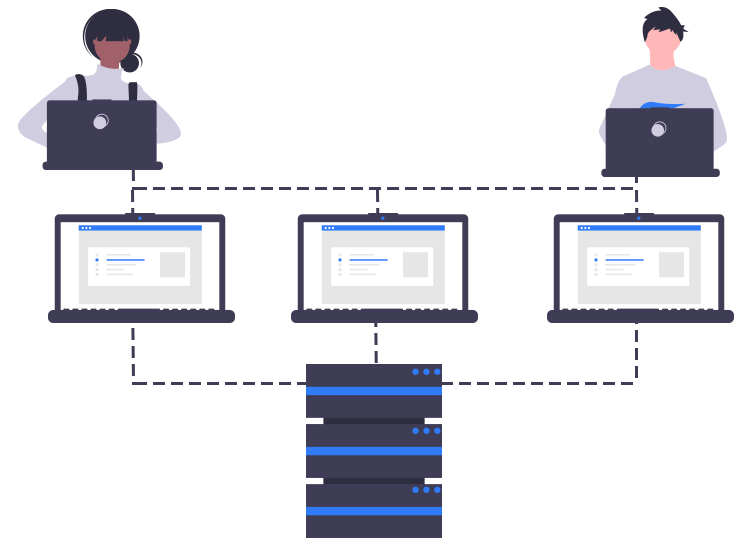
Since the IRC channel consists of numerous channels it provides a ready platform for the cyber-security criminals to carry their destructive activities. To spread the IRC worm drops scripts to the IRC client directory to establish a connection with the related IRC network. With the help of the installed script, the compromised client system is used by hackers to spread the infected files to other users on the same channel.
An Internet Relay Chat worm to work properly requires the client to confirm, access, and save the infected file. Due to this working methodology of IRC worm, it falls in the medium category in terms of severity and risk.
It is also noticed that the IRC worm exploits the mIRC network to spread itself. As against the IRC network in mIRC, the worm does not need user permissions to send and install copies of the infected file.
What adds on to the severity of IRC worm is that once it has infected a client’s system it can open backdoors to install other malicious malware on the device causing more damage.
Irrespective of the effectiveness of this harmful worm, it is extremely important that you follow all the precautionary measures to safeguard your device. Here are some of the effective yet simple ways to prevent Internet Relay Chat Worm.
Protection and preventive measures
- Ensure that your antivirus programs and operating system are up-to-date and patched against all security voids.
- Be fully sure while accessing emails from unknown sources they are often infected with malicious malware and can result in a compromised device.
- Try and have a good idea of the kind of malware attacks, this will help you take the necessary actions in time.
- Use a strong Ad-blocker and Firewall mechanism to save yourself from visiting third-party websites. This will also help you in spotting and eliminating malware that tries to enter your device.

